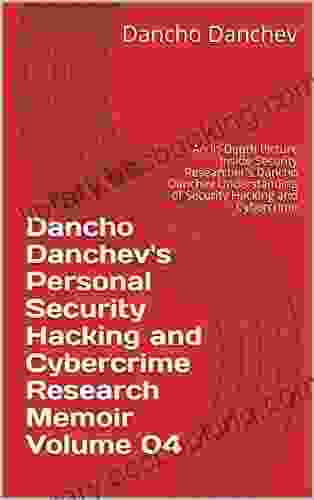
An In-Depth Look Inside Security Researcher Dancho Danchev's Understanding of Information Security


In his book, Danchev provides a comprehensive overview of the field of information security. He covers a wide range of topics, including:
- The basics of information security
- The different types of security threats
- The methods used to protect against security threats
- The legal and ethical implications of information security
Danchev's book is an essential resource for anyone who wants to learn more about information security. It is written in a clear and concise style, and it is packed with valuable information.
4.1 out of 5
| Language | : | English |
| File size | : | 68136 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 506 pages |
| Lending | : | Enabled |
Here is a more detailed look at some of the topics covered in Danchev's book:
The Basics of Information Security
Danchev begins his book by providing a brief overview of the basics of information security. He defines information security as "the protection of information from unauthorized access, use, disclosure, disruption, modification, or destruction." He then discusses the different types of information that can be protected, including:
- Data
- Applications
- Systems
- Networks
Danchev also discusses the different types of security threats that can face information systems. These threats include:
- Malware
- Hackers
- Spam
- Phishing
- Social engineering
Danchev concludes his discussion of the basics of information security by providing a brief overview of the methods used to protect against security threats. These methods include:
- Access control
- Encryption
- Firewalls
- Intrusion detection systems
- Disaster recovery
The Different Types of Security Threats
In the second chapter of his book, Danchev discusses the different types of security threats in more detail. He begins by providing a taxonomy of security threats. This taxonomy classifies security threats based on their target, their source, and their impact.
Danchev then discusses each type of security threat in more detail. He provides examples of each type of threat, and he explains how each threat can be mitigated.
The different types of security threats discussed in Danchev's book include:
- Malware
- Hackers
- Spam
- Phishing
- Social engineering
- Denial of service
- Man-in-the-middle
- Eavesdropping
- Spoofing
- Tampering
The Methods Used to Protect Against Security Threats
In the third chapter of his book, Danchev discusses the methods used to protect against security threats. He begins by providing a brief overview of the different types of security controls. These controls include:
- Physical security controls
- Technical security controls
- Administrative security controls
Danchev then discusses each type of security control in more detail. He provides examples of each type of control, and he explains how each control can be implemented.
The different types of security controls discussed in Danchev's book include:
- Access control
- Encryption
- Firewalls
- Intrusion detection systems
- Disaster recovery
Danchev concludes his discussion of the methods used to protect against security threats by providing a brief overview of the security risk management process. This process involves identifying, assessing, and mitigating security risks.
The Legal and Ethical Implications of Information Security
In the fourth chapter of his book, Danchev discusses the legal and ethical implications of information security. He begins by providing a brief overview of the different laws and regulations that govern information security. These laws and regulations include:
- The Computer Fraud and Abuse Act (CFAA)
- The Gramm-Leach-Bliley Act (GLBA)
- The Health Insurance Portability and Accountability Act (HIPPA)
Danchev then discusses the different ethical issues that can arise in the context of information security. These issues include:
- The privacy of personal data
- The security of critical infrastructure
- The use of surveillance technologies
Danchev concludes his discussion of the legal and ethical implications of information security by providing a brief overview of the ethical principles that should guide the practice of information security. These principles include:
- Confidentiality
- Integrity
- Availability
- Accountability
Dancho Danchev's book, "Information Security: A Comprehensive Guide," is an essential resource for anyone who wants to learn more about information security. It is written in a clear and concise style, and it is packed with valuable information. If you are interested in learning more about information security, I highly recommend reading Danchev's book.
Dancho Danchev's book, "Information Security: A Comprehensive Guide," is a valuable resource for anyone who wants to learn more about information security. It is a comprehensive and well-written book that covers a wide range of topics. I highly recommend this book to anyone who is interested in learning more about information security.
4.1 out of 5
| Language | : | English |
| File size | : | 68136 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 506 pages |
| Lending | : | Enabled |
Do you want to contribute by writing guest posts on this blog?
Please contact us and send us a resume of previous articles that you have written.
 Book
Book Novel
Novel Page
Page Chapter
Chapter Text
Text Story
Story Genre
Genre Reader
Reader Library
Library Paperback
Paperback E-book
E-book Magazine
Magazine Newspaper
Newspaper Paragraph
Paragraph Sentence
Sentence Bookmark
Bookmark Shelf
Shelf Glossary
Glossary Bibliography
Bibliography Foreword
Foreword Preface
Preface Synopsis
Synopsis Annotation
Annotation Footnote
Footnote Manuscript
Manuscript Scroll
Scroll Codex
Codex Tome
Tome Bestseller
Bestseller Classics
Classics Library card
Library card Narrative
Narrative Biography
Biography Autobiography
Autobiography Memoir
Memoir Reference
Reference Encyclopedia
Encyclopedia Thomas F King
Thomas F King Steven Alan Childress
Steven Alan Childress Sandra Lawrence
Sandra Lawrence Leif Holmvall
Leif Holmvall Pat Grillo
Pat Grillo Sun Tzu
Sun Tzu Sam W Haynes
Sam W Haynes Mark Blyth
Mark Blyth Liliana Maria Isella
Liliana Maria Isella Patrick Schulte
Patrick Schulte Roddy Scheer
Roddy Scheer Michael Banton
Michael Banton Nicole Seymour
Nicole Seymour Naomi Hirahara
Naomi Hirahara Mara Jaye
Mara Jaye Peter Dickinson
Peter Dickinson Mo Rocca
Mo Rocca Tim Notier
Tim Notier Piri Halasz
Piri Halasz Oliver Sin
Oliver Sin
Light bulbAdvertise smarter! Our strategic ad space ensures maximum exposure. Reserve your spot today!
 Harry CookFollow ·18.7k
Harry CookFollow ·18.7k Andres CarterFollow ·11k
Andres CarterFollow ·11k Jessie CoxFollow ·7k
Jessie CoxFollow ·7k Eli BlairFollow ·15.8k
Eli BlairFollow ·15.8k Andy ColeFollow ·6.3k
Andy ColeFollow ·6.3k Israel BellFollow ·10.7k
Israel BellFollow ·10.7k Darrell PowellFollow ·15.9k
Darrell PowellFollow ·15.9k Matt ReedFollow ·17.4k
Matt ReedFollow ·17.4k
 Brian Bell
Brian BellExploring The Natural World Through Mindful Expressive...
Unleash the...
 David Baldacci
David BaldacciJourney into the Enigmatic World of "Grass" by Sheri S....
Prepare to be captivated by "Grass," a...
 Dashawn Hayes
Dashawn HayesBusting Myths About Human Nature: Unraveling the Complex...
Challenging the...
 Ernest Hemingway
Ernest HemingwayNotes on Suicide: A Profound Exploration of the...
Suicide, a taboo subject shrouded in...
4.1 out of 5
| Language | : | English |
| File size | : | 68136 KB |
| Text-to-Speech | : | Enabled |
| Screen Reader | : | Supported |
| Enhanced typesetting | : | Enabled |
| Print length | : | 506 pages |
| Lending | : | Enabled |